 1-800-805-5783
1-800-805-5783 
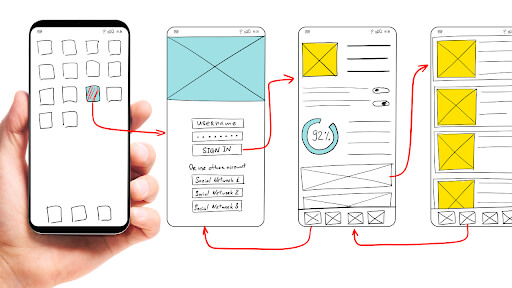
The era of technology and smartphones is currently upon us. Our real lives now include mobile phones, and in addition to communication, many apps available can dramatically ease our daily lives. The mobile app is the most reliable and accessible medium for value exchange between brands and clients. In light of this, users may legitimately expect a secure app environment for their interactions, and developers must provide applications with the most modern built-in in-app security. Consequently, it is now more important to consider mobile application security and protect users’ critical information.
Mobile app security entails protecting iOS and Android applications from intrusions by malicious attackers and identifying any system risks while the app is still being designed and in real time after it has been launched. To harden the application against actual threats and stop new potential vulnerabilities, comprehensive mobile app security integrates security technology with standard practices from the application security field. Many businesses increasingly use mobile applications for teamwork and customer and employee communication. Now more than ever, mobile apps have access to a lot of sensitive data that needs to be secured by employing all-encompassing mobile application security.
In plain text, insecure data storage vulnerabilities occur when applications store highly confidential information such as usernames, passwords, and credit card numbers. We require a robust security system to hold this sort of data. At most, one individual could suffer data loss due to insecure data storage.
Whenever the quantity of simultaneous web traffic, or load, strikes the web server, a web server’s capacity to sustain a site’s availability, durability, and performance is termed scalability. Client-side cyberattacks target desktop software in particular. An attacker’s top priorities are programs like web browsers, media players, email clients, office suites, and other similar programs.
Any information intended to be shielded from illegal access is termed sensitive data. Anything from personally identifying information, such as Social Security numbers, account records, and login credentials, might be classified as sensitive data. Users risk having their sensitive data compromised when a hacker gets access to this data due to a data breach. The targets of sensitive data exposure are genetic data, biometric data processed only to identify a human being, health-related data, and facts about a person’s sexual life or orientation.
Log monitoring is vital for a variety of reasons. One of the reasons seems to be that it can protect your servers and websites from going offline. Organizations need help figuring out what happens when a hostile insider with legitimate motives for accessing databases, using apps, changing system configurations, and obscuring information enters the system. Therefore, information about logging user access is essential for safeguarding data and averting data breaches.
Phishing is a fraud in which a perpetrator uses the internet or other contact forms to pose as a reliable organization or individual. Attackers typically employ phishing emails to propagate malicious URLs or attachments that can perform several tasks. Some will use their victims to obtain login details or account information. Phishing is using email, text messages, or even phone calls to trick a target into divulging a password, clicking a link to download malware, or confirming a transaction.
Here, we explore some frequently used tactics to encrypt user data in apps.
Documentation, websites, books, blogs, movies, photos, podcasts, and other media from other sources are included in this list. You don’t replicate from Wikipedia, dictionaries, or journals. It is worth looking for a team of developers with a track record of producing top-notch apps by employing a secure code source to avoid putting your app at risk and ensure high security.

API integration should be approached with prudence. If not implemented correctly, it could lead to a poor user experience and application performance. The following suggestions can assist you in integrating APIs productively. Ensure your APIs are robust against common security risks and data theft. By integrating tried-and-true APIs from credible vendors, you can manage your important apps while providing a strong user experience.
Secure The App’s Backend.
To thwart automated assaults, use multi-factor authentication.
Encourage the user to adopt a strong password policy. Limit the number of failed login attempts. Use the hashing algorithm.
Compared to storage media in a cloud environment, storage media in a data center is considerably easier to monitor for security and illegal access. Developers prefer to put sensitive data in the device’s local memory to keep it hidden from consumers. While it’s best to avoid keeping your private information on your app and mobile device, you should employ encrypted data containers or key chains if there is no other choice. Add the auto-deleting feature, which defaults to delete data after a set amount of time, to limit the log further.
Use implicit intents with an app chooser, permissions based on identities, and non-exported content owners to communicate across apps more seamlessly. Use signature-based permissions to share data between two apps that you own or are in control of. These permissions ensure that the data-accessed apps are signed with the same signing key rather than requiring user confirmation. As a result, these permissions provide a more straightforward, safer user experience.
Employ an SDK to handle the management components to manage enterprise requirements such as social media integration and support, mobile app use cases, mobile app management, app development approaches, and more. The first step is understanding the client’s needs for administering the specific mobile app while considering mobile OS and platform-specific obstacles.
Now, think smarter: Is your smartphone only a caller ID or text messaging device? In actuality, no; since the demanding expansion of your company and the abundance of sensitive data you store there, it has become a prime target for theft via hackers. It would help if you acted appropriately to shield your smartphone and mobile app to prevent a mishap from striking. Take advantage of these tips on mobile app security, whether you have an existing mobile app or intend to develop one. Work with a mobile application development company that gives your business a competitive edge. It is the only way to deter hackers and improve customer experience.